FTC Safeguards Rule Compliance for Accounting Firms in 2026
The updated FTC Safeguards Rule has been in full effect since June 9, 2023. Tax preparers, CPAs, and bookkeepers are covered. Civil penalties reach $50,120 per violation. This is what compliance actually requires.
On this page
The FTC Safeguards Rule is not a recommendation. It is a legally binding federal regulation that applies to your accounting firm regardless of size, regardless of how long you have been in practice, and regardless of whether you have ever heard of it.
The updated rule — codified at 16 CFR Part 314 under the Gramm-Leach-Bliley Act — took full effect on June 9, 2023. Breach notification requirements followed in May 2024. If your firm prepares tax returns, manages payroll, or provides financial planning services for compensation, you are almost certainly a covered financial institution under this rule.
Enforcement is active
The FTC can impose civil penalties of up to $50,120 per violation (2025 inflation-adjusted figure under 15 U.S.C. § 45). Each missing safeguard constitutes a separate violation. The IRS can separately suspend or revoke a firm’s Electronic Filing Identification Number (EFIN) following a data breach — which effectively shuts down your ability to file returns electronically during tax season.
Who the rule covers
The most common misconception among small CPA firms and independent tax preparers is that the Safeguards Rule applies only to banks. The rule’s definition of “financial institution” under GLBA Section 6809(3) is deliberately broad. The FTC has specifically confirmed that the following business types are covered:
Covered entity types under the FTC Safeguards Rule
- Individual tax preparers holding a Preparer Tax Identification Number (PTIN) who prepare returns for compensation.
- CPA firms and accounting practices of any size — including sole proprietorships.
- Enrolled Agents (EAs) representing taxpayers before the IRS.
- Bookkeeping services that handle payroll or financial record preparation.
- Financial advisors who are not registered with the SEC.
- Firms providing financial planning, credit counseling, or tax resolution services.
There is a partial exemption for firms maintaining fewer than 5,000 customer records — but the IRS counts partner K-1s, former client records, and employee PII from your clients as part of that number. Most CPA firms exceed 5,000 records without realising it and should not rely on this exemption without a deliberate count.
870,679
individuals holding active Preparer Tax Identification Numbers in 2025 — every one of them is a covered entity under the Safeguards Rule
Source: IRS PTIN data, 2025The nine requirements your firm must meet
The Safeguards Rule is outcome-based — it does not prescribe specific technology. It prescribes nine requirements and leaves implementation to each firm, scaled to the firm’s size and the sensitivity of the data it handles.
The nine FTC Safeguards Rule requirements
1. Designate a qualified individual
Assign one person — an employee, officer, or qualified service provider — to own your information security program. For small firms, this is typically the managing partner. The designation must be documented. This person is accountable if the program fails.
2. Conduct a written risk assessment
Document the specific risks to client information in your environment. This means identifying where client data lives (email, cloud storage, tax software, physical files), who has access, and what controls exist. Risk assessments must be updated periodically — not completed once and filed.
3. Implement and document safeguards
Based on your risk assessment, implement controls that address the risks identified. These must be documented in a Written Information Security Plan (WISP). The WISP is both a compliance document and an operational guide. If you do not have one, creating it is your first priority.
4. Manage service providers
If any vendor handles client data — cloud storage, tax software, document portals, payroll processors — you must obtain written assurance of their security practices and periodically review their controls. A vendor data breach does not relieve your firm of liability.
5. Implement access controls
Client data must be accessible only to people who need it. This means multi-factor authentication for all remote access, role-based access controls, and documented procedures for revoking access when staff leave or change roles.
6. Encrypt data in transit and at rest
All client data transmitted over the internet must be encrypted (TLS 1.2+ is the current baseline). All client data stored — in cloud systems, on firm devices, or on backup drives — must be encrypted at rest. This is where email-based document collection fails categorically.
7. Conduct penetration testing and vulnerability assessments
Annual penetration testing and biannual vulnerability assessments are required. These must be conducted by a qualified third party, not internally, for firms with systems managing more than 5,000 records. Results must be documented and remediation tracked.
8. Implement multi-factor authentication
MFA is explicitly required for any individual accessing customer information systems remotely. This is not optional. The FTC has been clear that this requirement is non-negotiable for covered entities.
9. Establish an incident response plan
You must have a documented, tested plan for detecting, containing, and reporting security incidents. If a breach involves 500 or more customers, you must notify the FTC within 30 days of discovery. The plan must be tested, not just written.
Where most small firms are exposed
The rule has been in effect for three years. Most large accounting firms have completed compliance programs. The firms still exposed are small practices — sole practitioners, 2–10 person firms — that assumed the rule applied to banks, not bookkeepers.
Common compliance gaps in small accounting firms
| Requirement | Common failure mode | Consequence |
|---|---|---|
| WISP | Does not exist or was generated from a template and never tailored to the firm | Primary evidence of non-compliance in FTC review |
| Data encryption | Client documents collected and stored via email — no encryption at rest | Structural failure of the encryption requirement — every email thread is a gap |
| Vendor management | No written security agreements with tax software vendors, cloud storage providers, or client portals | Full liability for vendor breaches without documented due diligence |
| Access controls | Shared passwords for tax software, no MFA on remote access | MFA requirement violation — explicitly cited in FTC enforcement actions |
| Incident response | No documented response plan — firm would not know what to do within 30 days of a breach | Late FTC notification = additional daily penalty up to $43,792/day until resolved |
| Risk assessment | Completed once at launch, never updated as the firm added tools, staff, or clients | Stale assessments do not satisfy the periodic review requirement |
The email problem
The most structurally vulnerable part of most small firm compliance postures is document collection by email. This is not a minor gap. Email fails four of the nine Safeguards Rule requirements simultaneously.
How email fails the Safeguards Rule
0
encryption guarantee at rest
Documents sit in inboxes in plaintext, indefinitely, on servers you do not control.
0
access control enforcement
Once sent, an email attachment can be forwarded to anyone without your knowledge.
0
audit trail per document
No log of who accessed what, when, or from where — required for incident investigation.
∞
retention — no expiration
Sensitive documents persist forever unless manually deleted. Expanding attack surface with every new engagement.
This is the compliance argument for client portals, independent of the operational one. A purpose-built document collection system that uses TLS in transit, AES-256 at rest, access-scoped links with expiration, and a timestamped audit log per document satisfies all four of those requirements. Email does not satisfy any of them.
'Reasonable safeguards' is a legal standard
The Safeguards Rule requires “reasonable safeguards” — a standard the FTC interprets in light of current technology and industry practice. Email was not designed for secure document transport. In 2026, continuing to collect sensitive financial documents via email is increasingly difficult to defend as a “reasonable” choice when purpose-built alternatives exist.
Building your compliance program in four stages
For firms that are not yet compliant, or firms that have a WISP but have not verified it against current requirements, this is the practical sequence.
Compliance program build sequence
Week 1–2
Inventory and designate
Map every place client data currently lives: email, cloud drives, tax software, physical storage, backup drives. Designate your qualified individual in writing. You cannot manage risk you have not mapped.
Week 3–4
Conduct and document your risk assessment
For each data location, identify the risk (unauthorised access, interception in transit, accidental disclosure) and the control currently in place. Document gaps explicitly — these become your remediation list.
Week 5–8
Build and implement the WISP
Draft your Written Information Security Plan using the risk assessment output. The WISP must address all nine rule requirements, be tailored to your firm’s actual environment, and be reviewed annually. The AICPA and IRS Publication 5708 both publish WISP templates — use them as a starting framework, not a copy-paste solution.
Week 9–12
Close the technical gaps
Enable MFA on all systems with remote access to client data. Move document collection off email to a TLS + AES-256 portal. Obtain written security assurances from all vendors handling client data. Run your first vulnerability assessment.
Ongoing
Maintain, test, and update
Annual WISP review. Annual penetration test. Biannual vulnerability assessments. Access reviews when staff change. Incident response plan test at least once per year. Document everything — documentation is your first line of defence in an FTC inquiry.
Key resources for your compliance program
ftc.gov
FTC Safeguards Rule — Small Entity Compliance Guide
The official FTC guidance document for businesses covered by the Gramm-Leach-Bliley Safeguards Rule. The authoritative source for requirement interpretation.aicpa-cima.com
AICPA — GLBA and Safeguards Rule Resources
The AICPA's resource hub for CPA firms, including a WISP template and data security best practices guide.The compliance self-audit
Before your next client intake, run this checklist. Every unchecked item is a documented compliance gap.
FTC Safeguards Rule compliance self-audit
- A qualified individual is formally designated as the owner of our information security program.
- We have a written, current risk assessment that maps every location client data is stored or transmitted.
- We have a WISP that addresses all nine Safeguards Rule requirements and was reviewed in the past 12 months.
- All remote access to systems containing client data requires multi-factor authentication.
- Client data in transit is encrypted — TLS 1.2+ on all connections.
- Client data at rest is encrypted — AES-256 or equivalent on all storage systems.
- Client documents are not collected or stored via standard email.
- We have written security agreements with every vendor who handles client data.
- We have conducted a penetration test in the past 12 months (or biannual vulnerability assessment).
- We have a documented, tested incident response plan and know the 30-day FTC notification trigger.
- Access permissions are reviewed when staff join, change roles, or leave the firm.
Compliance is not a one-time project. It is an ongoing operational discipline. The firms that get into trouble are not the ones that tried and fell short on one requirement — they are the ones that treated the rule as someone else’s problem.
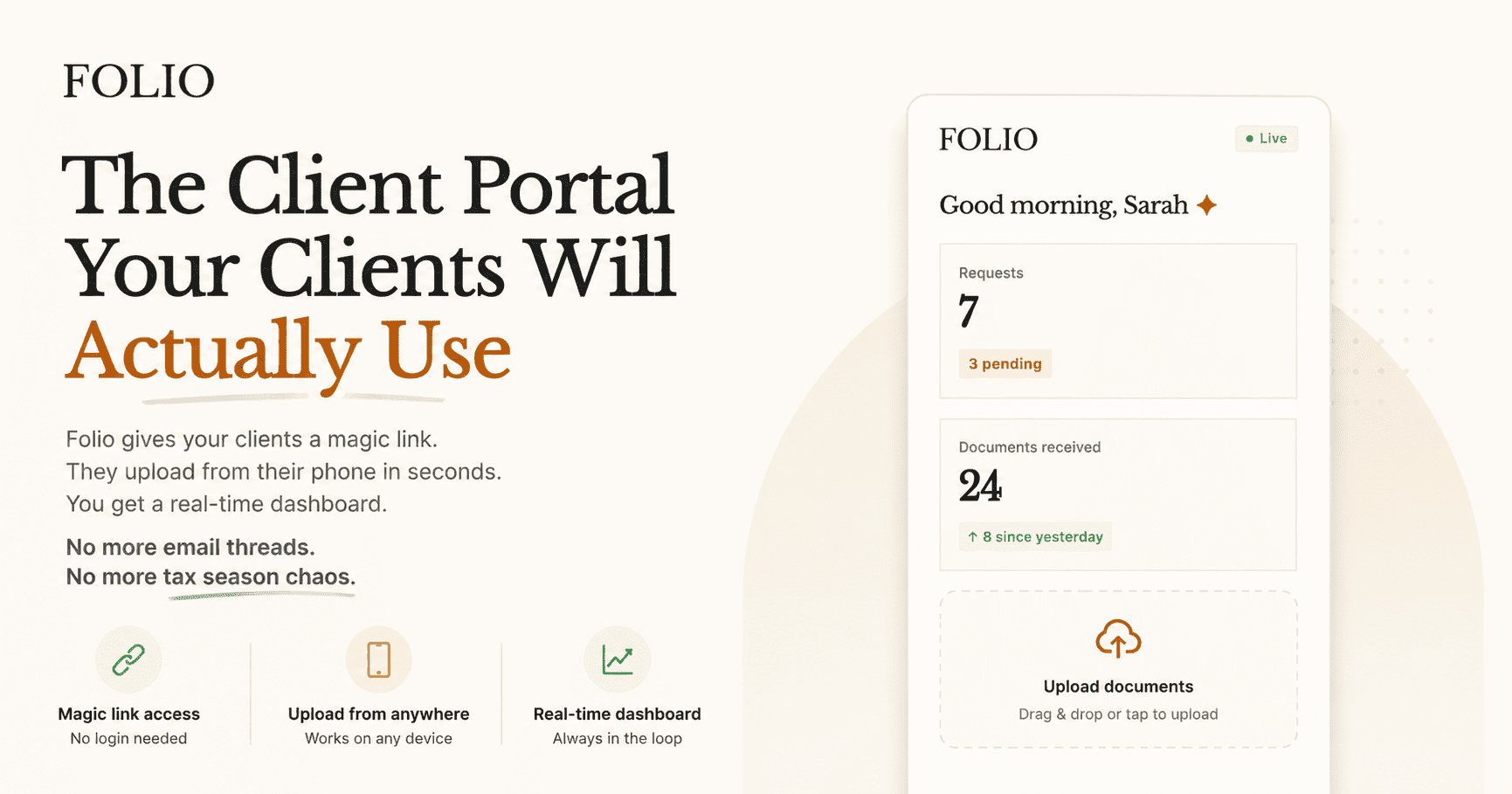
Folio helps close one of the most common compliance gaps
Collecting client documents through email is the most structurally exposed practice for small accounting firms. Folio replaces it with a TLS + AES-256 encrypted collection layer, access-scoped magic links with expiration, and a timestamped audit log per document — the controls the Safeguards Rule requires.
Frequently asked questions
Does the Safeguards Rule apply to my firm if I have fewer than 10 clients?
Almost certainly yes. The rule covers any firm “significantly engaged” in financial services — which includes any tax preparer working for compensation, regardless of client count. The partial exemption for fewer than 5,000 customer records reduces some requirements, but does not eliminate the need for a WISP, encryption, access controls, or MFA.
What is a WISP and do I actually need one?
A Written Information Security Plan is a documented description of your firm’s safeguards for protecting client data. The Safeguards Rule explicitly requires it. The IRS also requires it for all tax preparation firms under its own cybersecurity guidance (IRS Publication 4557 and Publication 5708). If you do not have one, creating it is the single highest-priority compliance action.
Can I use a generic WISP template?
You can use a template as a starting point, but it must be tailored to your firm’s actual systems, data locations, team size, and vendor relationships. A generic template that does not reflect your environment is not compliant — it is documentation theater. The AICPA and IRS both provide templates designed for accounting firms.
What happens if there is a breach before I am fully compliant?
The FTC will look at what controls were in place at the time of the breach and whether the firm had a reasonable program. A partially complete compliance program is far better than none. Document everything you have done, even if incomplete — documentation of good-faith effort matters in regulatory review.
Does my cloud tax software count as encrypted storage?
It depends on the vendor’s implementation. The Safeguards Rule requires that you verify and document your vendor’s security practices — you cannot assume encrypted storage without written confirmation. Request a SOC 2 Type II report or equivalent security documentation from every vendor handling client data.
Stay close
Secure document collection from day one
Folio provides TLS in transit, AES-256 at rest, access-scoped magic links, and a full document audit trail — without requiring clients to create accounts or install software.
See our security postureRelated posts
Why Accountants Switch from Email to Client Portals
Email works until it does not. The switch happens when firms measure what chasing actually costs in hours, errors, and lost clients.
Read article →Secure Document Collection for Accounting Firms
Email is not a secure document transport. Accounting firms handling sensitive financial data need collection infrastructure that meets compliance requirements without adding client friction.
Read article →